Security in every line, so you can code without compromise
.webp)
World-class teams choose Endor Labs

.webp)
How it works
.webp)
.webp)
.webp)
Unmatched code security intelligence
Your Tools, Your Languages
— All Secured
Built for teams that code without compromise
Resources
FAQs
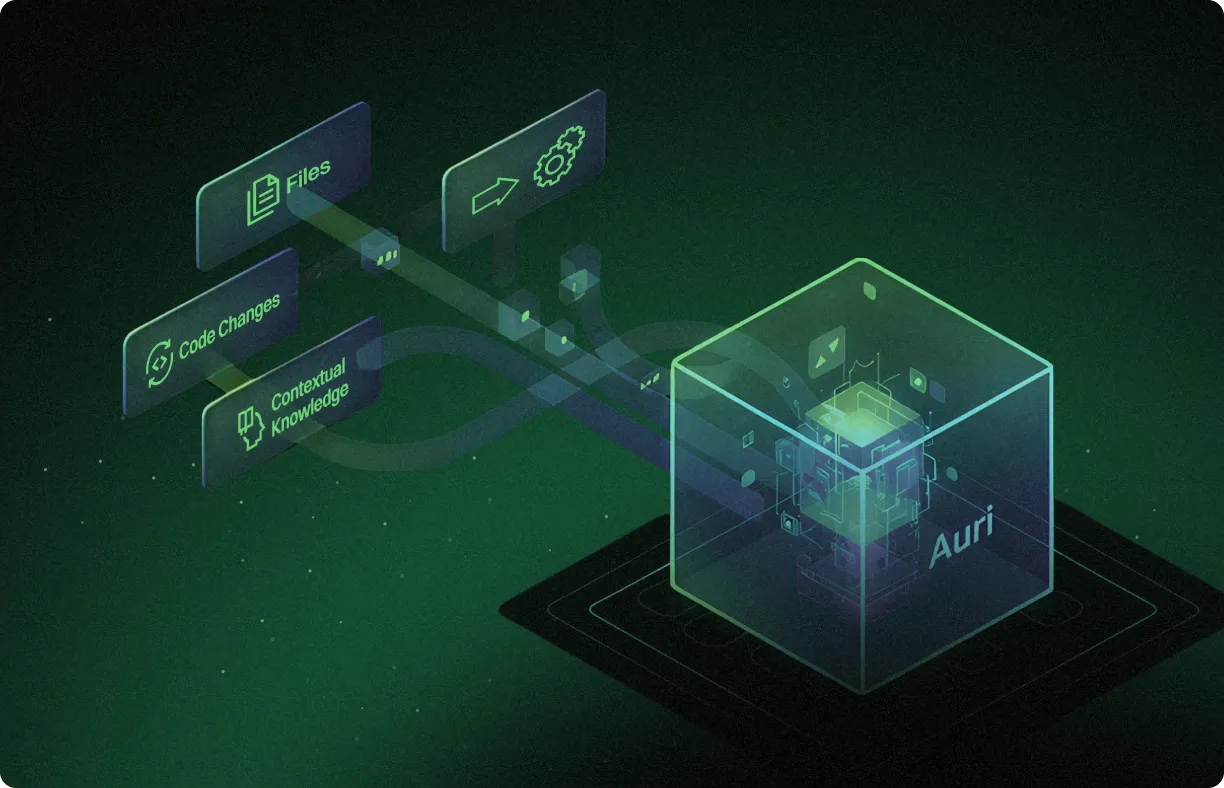
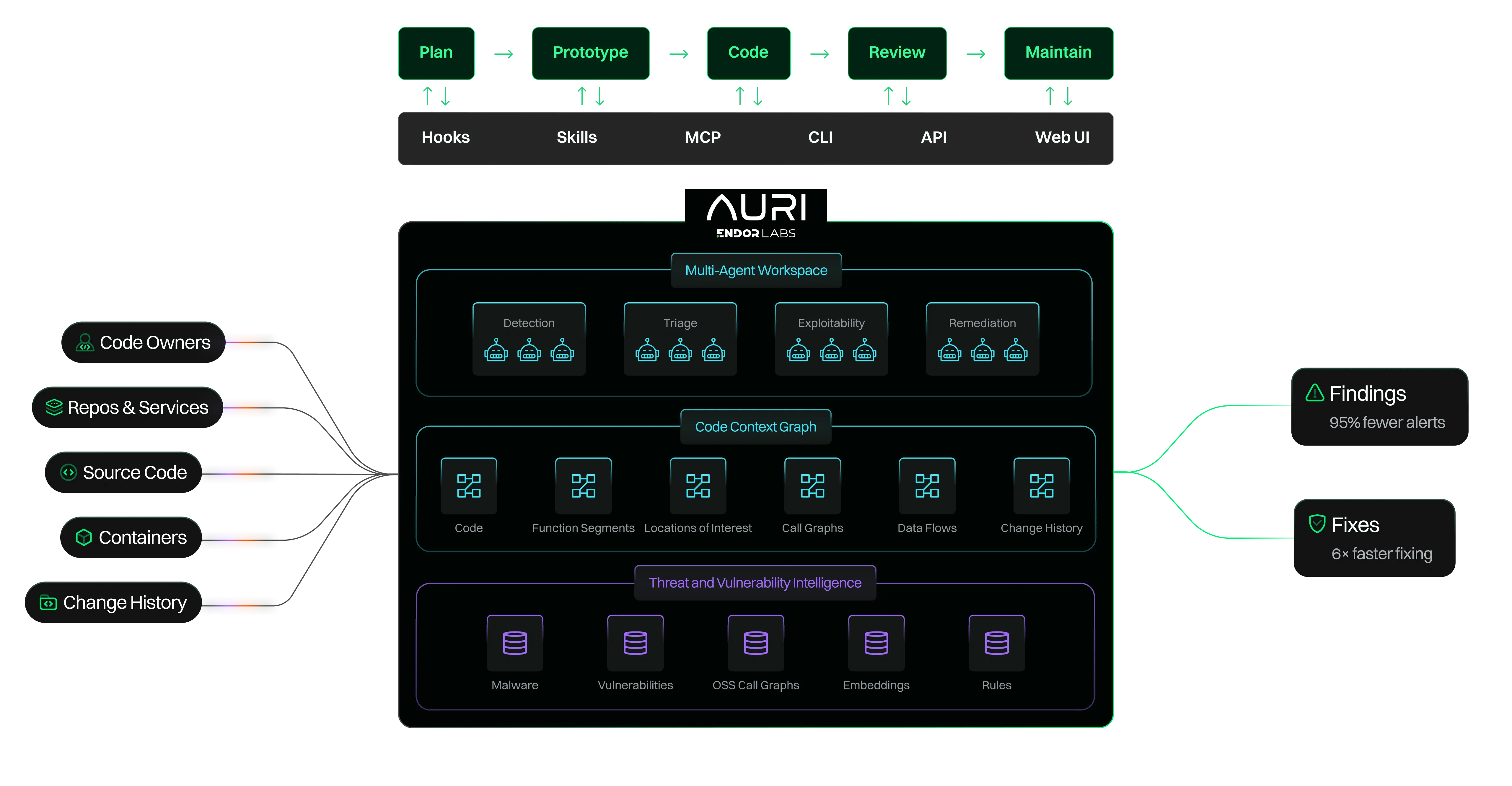
AURI by Endor Labs is an AI-native application security platform built for agentic software development. It equips security agents with the tools, skills, and context they need to find vulnerabilities, validate they're real, and fix them — all within your existing development workflows. At its core is a code context graph that maps how your code, dependencies, container images, and services actually connect.
Traditional AppSec tools — SAST scanners, SCA tools, and vulnerability management platforms — flag alerts without understanding your application's actual architecture. They can't tell whether a vulnerability is reachable, whether upstream middleware already mitigates a finding, or what a valid fix looks like in your specific codebase. AURI’s proprietary code context graph combines deep program analysis, proprietary threat intelligence, and agentic AI reasoning to deliver evidence-backed findings instead of alert noise, and can autonomously remediate the issues it finds.
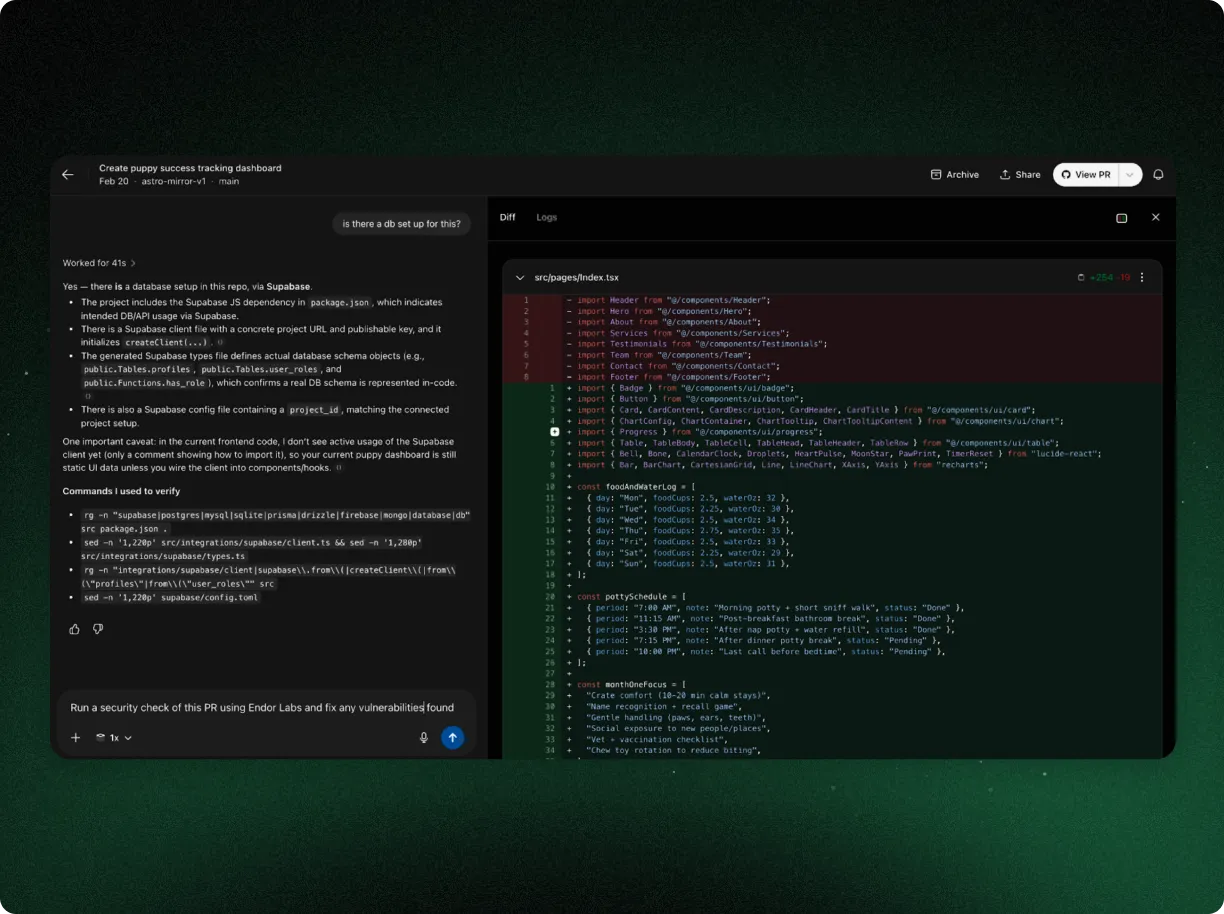
AI coding agents can write code, but lack security context — they can't see how your full application connects. AURI provides the missing security intelligence layer. It monitors code generated by AI agents, validates it against your application's architecture, catches vulnerabilities that single-file analysis would miss, and works directly with your coding agent to apply fixes. Think of AURI as the security intelligence your AI coding agent is missing.
AURI integrates with popular IDEs and coding tools including Cursor, Windsurf, VS Code, and Claude Code via MCP, Skills, and CLI. It plugs into your CI/CD pipeline via API and supports analysis across first-party code, open-source dependencies, and container images. For specific language and framework support details, contact our team or check the documentation.
Yes. AURI's autonomous remediation capability goes beyond flagging issues. When it identifies a real vulnerability, it already understands where the affected code is used, whether the vulnerable paths are reachable, and what a valid fix looks like in your specific codebase. It works directly with your coding agent to apply patches and refactor code to avoid breaking changes — without pulling developers off feature work.
AURI uses an LLM-native malicious package detection pipeline that analyzes package behavior the way a senior security researcher would — examining install scripts, obfuscation patterns, network calls, and data exfiltration signals in context. Unlike traditional YARA rule-based detection, which suffers from high false positive rates, AURI can scan and analyze any OSS package within two minutes at 99% accuracy. It catches threats like typosquatting, dependency confusion, and obfuscated exfiltration scripts before your agent ever imports them.
The code context graph is AURI's foundational technology. It's a deep representation of how your application actually works — mapping first-party code, open-source dependencies, container images, and data flows into a unified model. It's powered by purpose-built program analysis tools (call graph analysis, data flow analysis, code summarization, and code navigation) combined with proprietary vulnerability and threat intelligence at the function level. This graph is what allows AURI to reason about your application with the same depth as a senior security engineer.
Yes. AURI's MCP, Skills, and CLI are free for developers to install and start using immediately. You can add AURI to your editor in minutes and start writing more secure code. For enterprise teams that need AURI's full platform — including organization-wide policies, governance, and integrations — contact us to book a demo.
Most security backlogs grow because teams can't distinguish real risk from scanner noise, and fixing requires manual developer context-switching. AURI attacks this from both sides: it eliminates up to 95% of false positives so your backlog only contains real issues, and its autonomous remediation applies validated fixes inside your existing workflows. Teams can burn down backlogs that have been growing for years without pulling developers off feature work.
Start shipping with confidence














%20(1).avif)



.webp)

